I’ve been a long time Google Chrome user, but Chrome’s lack of certificate revocation checking persuaded me to switch to Firefox as my secure browser. I’ve relegated Chrome to being my media browser to take advantage of it’s built in and automatically updated Flash player.
After a few days back on Firefox, I’m happy with the switch. Firefox’s certificate revocation checking seems to be faster than Chrome’s (completely subjective) and Firefox’s security is much easier to customize.
Transition Process
Add-Ons
under Settings → Add-Ons, I added:
- LastPass – works about the same, but seems to be slightly less stable
- NoScript – more mature than ScriptSafe
- CipherFox – provides ciphersuite information in a dropdown and allows easy enabling and disabling of RC4 based ciphersuites (check "Disable RC4 cipher" in the Extension preferences).
I also installed HTTPS Everywhere. It seems to be more mature and easier to manage than the Chrome version, with the exception of adding custom rules. Custom rules must be added to a folder in the filesystem and cannot be edited from within Firefox.
Plugins
Under Settings → Add-Ons → Plugins
I set all of my media plugins like Google Talk and Microsoft Silverlight to "Ask to Activate".
I set to Java (it got installed when I was doing some Java development) to "Never Activate".
Preferences/Options
Under Advanced → Data Choices, I disabled Firefox Health Report and Crash Reporter, because these could inadvertently disclose sensitive information.
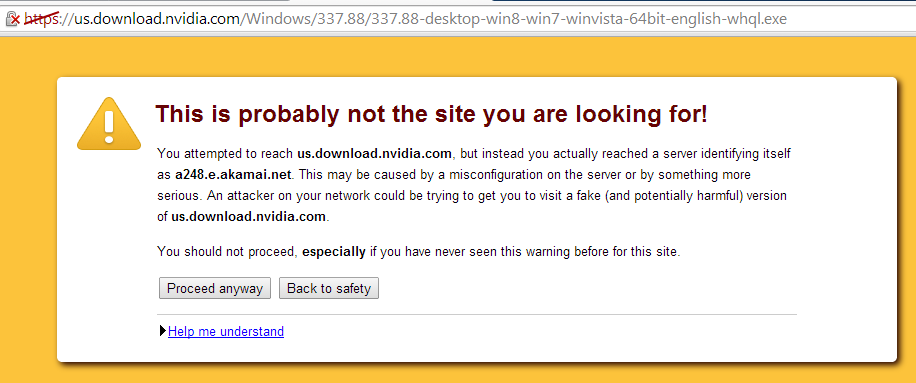
Under Advanced → Certificates, click the Validation button and check "When an OCSP server connection fails, treat the certificate as invalid".
Advanced Configuration
Type "about:config" into the address bar.
- Disable SSLv3.0
- security.tls.version.min = 1
- Disable DSS based authentication
- security.ssl3.dhe_dss_aes_128_sha = false
- security.ssl3.dhe_dss_aes_256_sha = false
- Disable Triple DES based ciphersuites
- security.ssl3.dhe_rsa_des_ede3_sha = false
- security.ssl3.ecdhe_rsa_des_ede3_sha = false
- security.ssl3.dhe_rsa_des_ede3_sha = false
- security.ssl3.ecdhe_rsa_des_ede3_sha = false
- security.ssl3.rsa_des_ede3_sha = false
- Minimize Session Data Storage
- browser.sessionstore.restore_on_demand = false
- browser.sessionstore.resume_from_crash = false
Summary
These configurations give you good control over what runs on each page through NoScript and Ask to Activate.
The most sites use RSA or ECDSA certificates and support AES. I generally find that sites that don’t support AES, only support RC4, so disabling Tripple DES doesn’t reduce compatibility. I use CipherFox to enable RC4 on an as-needed basis, because some sites that support AES, prioritize RC4 (e.g. BarclayCard). Due to Dreamhost’s server configuration, this site only supports RC4.
At this point, I rarely encounter a site that does not support at least TLSv1.0, so I figure it’s time to disable SSLv3.0.