dnscrypt-proxy has a lot of features and can be intimidating to setup. Issues range from understanding what dnscrypt is to how to pick list of sources to understanding what a stamp is.
While it’s not a recommended configuration, I wanted to setup a very simple/minimal dnscrypt-proxy that uses a few well known DoH servers.
Steps
- Install dnscrypt-proxy.
- Edit the configuration file (/etc/dnscrypt-proxy.toml or /etc/dnscrypt-proxy/dnscrypt-proxy.toml on Linux/UNIX systems).
- Delete or comment out server_names
![# server_names = ['scaleway-fr', 'google', 'yandex', 'cloudflare']](https://www.tidgubi.com/wp-content/uploads/2021/02/Screen-Shot-2021-02-06-at-6.20.48-PM-1.png)
- Delete or comment out the entries under [sources]
![[sources]](https://www.tidgubi.com/wp-content/uploads/2021/02/Screen-Shot-2021-02-06-at-6.25.52-PM.png)
- If present, ensure doh_servers = true
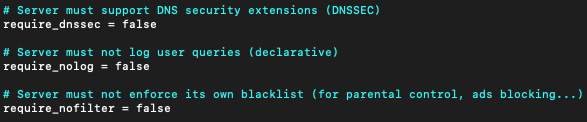
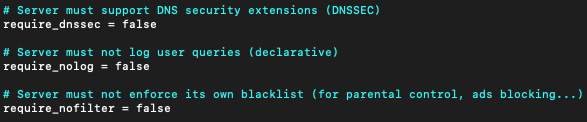
- Depending on the servers you configure, you might need to edit require_dnssec, require_nolog, and require_nofilter to be compatible with the servers. Since I’m explicitly configuring a small list of servers, it’s easier to turn off all restrictions
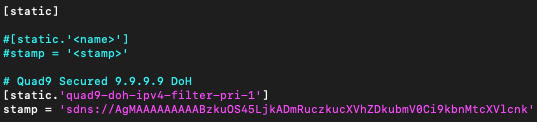
- Add your desired servers to the [static] section (for this you should get a basic understanding of stamps)
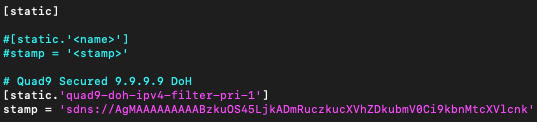
Note: each static entry requires a unique name.
Stamps
While you don’t need a detailed understanding of stamps, it’s good to have a basic understanding; so you can audit the servers you are adding and you can add custom servers.
A stamp is just dnscrypt-proxy’s format for encoding all relevant parameters for a DNS server. For a DoH server, that consists of:
- Properties (required) – flags indicating if the server is DNSSEC capable, logs queries, or filters results.
- IP address (optional) – If an IP address is not provided the Host will be used.
Note: The spec says the port (if not 443) should be provided in this field; however, the public lists and the stamp calculator include the port in the Host field - Host (required) – self-explanatory
- Hashes (optional) – doesn’t appear to be working. This should allow trusting custom cert chains; however, dnscrypt-proxy is only using the platform’s trust store to validate certificate chains.
- Path (required) – for DoH servers this is generally “/dns-query”. This should be well documented with the information about each DoH server.
You have three options:
- Generate your own stamps using the stamp calculator
- Use stamps below
- Copy stamps from a public list:
For any pre-generated stamps, you can check the contents by pasting the stamp into to Stamp field of the stamp calculator.
DoH Server Stamps
Some stamps for common DoH servers. While I have verified these stamps work, I make no claim to the accuracy of the properties.
Quad9
Ref: https://quad9.net/doh-quad9-dns-servers/
Properties: DNSSEC, Filter (malicious domain blocking), No Logging (limited per the Quad9 FAQ):
# Quad9 Secured 9.9.9.9 DoH
[static.'quad9-doh-ipv4-filter-pri-1']
stamp = 'sdns://AgMAAAAAAAAABzkuOS45LjkADmRuczkucXVhZDkubmV0Ci9kbnMtcXVlcnk'
# Quad9 Secured 149.112.112.9 DoH
[static.'quad9-doh-ipv4-filter-pri-2']
stamp = 'sdns://AgMAAAAAAAAADTE0OS4xMTIuMTEyLjkADmRuczkucXVhZDkubmV0Ci9kbnMtcXVlcnk'
# Quad9 Secured 2620:fe::9 DoH
[static.'quad9-doh-ipv6-filter-pri-1']
stamp = 'sdns://AgMAAAAAAAAADFsyNjIwOmZlOjo5XQAOZG5zOS5xdWFkOS5uZXQKL2Rucy1xdWVyeQ'
# Quad9 Secured 2620:fe::fe:9 DoH
[static.'quad9-doh-ipv6-filter-pri-2']
stamp = 'sdns://AgMAAAAAAAAAD1syNjIwOmZlOjpmZTo5XQAOZG5zOS5xdWFkOS5uZXQKL2Rucy1xdWVyeQ'
Properties: DNSSEC, No Filter, No Logging (limited per the Quad9 FAQ):
# Quad9 Unsecured 9.9.9.10 DoH
[static.'quad9-doh-ipv4-nofilter-pri-1']
stamp = 'sdns://AgMAAAAAAAAACDkuOS45LjEwAA9kbnMxMC5xdWFkOS5uZXQKL2Rucy1xdWVyeQ'
# Quad9 Unsecured 149.112.112.10 DoH
[static.'quad9-doh-ipv4-nofilter-pri-2']
stamp = 'sdns://AgMAAAAAAAAADjE0OS4xMTIuMTEyLjEwAA9kbnMxMC5xdWFkOS5uZXQKL2Rucy1xdWVyeQ'
# Quad9 Unsecured 2620:fe::10 DoH
[static.'quad9-doh-ipv6-nofilter-pri-1']
stamp = 'sdns://AgMAAAAAAAAADVsyNjIwOmZlOjoxMF0AD2RuczEwLnF1YWQ5Lm5ldAovZG5zLXF1ZXJ5'
# Quad9 Unsecured 2620:fe::fe:10 DoH
[static.'quad9-doh-ipv6-nofilter-pri-2']
stamp = 'sdns://AgMAAAAAAAAAEFsyNjIwOmZlOjpmZToxMF0AD2RuczEwLnF1YWQ5Lm5ldAovZG5zLXF1ZXJ5'
Cloudflare DNS
Ref: https://developers.cloudflare.com/1.1.1.1/1.1.1.1-for-families
Properties: DNSSEC, Filter (malicious content blocking), No Logging (limited per Privacy):
# Cloudflare Security 1.1.1.2 DoH
[static.'cloudflare-doh-ipv4-filter-pri-1']
stamp = 'sdns://AgMAAAAAAAAABzEuMS4xLjIAG3NlY3VyaXR5LmNsb3VkZmxhcmUtZG5zLmNvbQovZG5zLXF1ZXJ5'
# Cloudflare Security 1.0.0.2 DoH
[static.'cloudflare-doh-ipv4-filter-pri-2']
stamp = 'sdns://AgMAAAAAAAAABzEuMC4wLjIAG3NlY3VyaXR5LmNsb3VkZmxhcmUtZG5zLmNvbQovZG5zLXF1ZXJ5'
# Cloudflare Security 2606:4700:4700::1112 DoH
[static.'cloudflare-doh-ipv6-filter-pri-1']
stamp = 'sdns://AgMAAAAAAAAAFlsyNjA2OjQ3MDA6NDcwMDo6MTExMl0AG3NlY3VyaXR5LmNsb3VkZmxhcmUtZG5zLmNvbQovZG5zLXF1ZXJ5'
# Cloudflare Security 2606:4700:4700::1002 DoH
[static.'cloudflare-doh-ipv6-filter-pri-2']
stamp = 'sdns://AgMAAAAAAAAAFlsyNjA2OjQ3MDA6NDcwMDo6MTAwMl0AG3NlY3VyaXR5LmNsb3VkZmxhcmUtZG5zLmNvbQovZG5zLXF1ZXJ5'
Properties: DNSSEC, No Filter, No Logging (limited per Privacy):
# Cloudflare DNS 1.1.1.1 DoH
[static.'cloudflare-doh-ipv4-nofilter-pri-1']
stamp = 'sdns://AgMAAAAAAAAABzEuMS4xLjEAEmNsb3VkZmxhcmUtZG5zLmNvbQovZG5zLXF1ZXJ5'
# Cloudflare DNS 1.0.0.1 DoH
[static.'cloudflare-doh-ipv4-nofilter-pri-2']
stamp = 'sdns://AgMAAAAAAAAABzEuMC4wLjEAEmNsb3VkZmxhcmUtZG5zLmNvbQovZG5zLXF1ZXJ5'
# Cloudflare DNS 2606:4700:4700::1111 DoH
[static.'cloudflare-doh-ipv6-nofilter-pri-1']
stamp = 'sdns://AgMAAAAAAAAAFlsyNjA2OjQ3MDA6NDcwMDo6MTExMV0AEmNsb3VkZmxhcmUtZG5zLmNvbQovZG5zLXF1ZXJ5'
# Cloudflare DNS 2606:4700:4700::1001 DoH
[static.'cloudflare-doh-ipv6-nofilter-pri-2']
stamp = 'sdns://AgMAAAAAAAAAFlsyNjA2OjQ3MDA6NDcwMDo6MTAwMV0AEmNsb3VkZmxhcmUtZG5zLmNvbQovZG5zLXF1ZXJ5'
Google DNS
Ref: https://developers.google.com/speed/public-dns/docs/doh
Properties: DNSSEC, No Filter, Logging (generally full logs are only temporary per the Privacy Statement):
# Google DNS 8.8.8.8 DoH
[static.'google-doh-ipv4-nofilter-1']
stamp = 'sdns://AgMAAAAAAAAABzguOC44LjgACmRucy5nb29nbGUKL2Rucy1xdWVyeQ'
# Google DNS 8.8.4.4 DoH
[static.'google-doh-ipv4-nofilter-2']
stamp = 'sdns://AgMAAAAAAAAABzguOC40LjQACmRucy5nb29nbGUKL2Rucy1xdWVyeQ'
# Google DNS 2001:4860:4860::8888 DoH
[static.'google-doh-ipv6-nofilter-1']
stamp = 'sdns://AgMAAAAAAAAAFlsyMDAxOjQ4NjA6NDg2MDo6ODg4OF0ACmRucy5nb29nbGUKL2Rucy1xdWVyeQ'
# Google DNS 2001:4860:4860::8844 DoH
[static.'google-doh-ipv6-nofilter-2']
stamp = 'sdns://AgMAAAAAAAAAFlsyMDAxOjQ4NjA6NDg2MDo6ODg0NF0ACmRucy5nb29nbGUKL2Rucy1xdWVyeQ'
![[sources]](https://www.tidgubi.com/wp-content/uploads/2021/02/Screen-Shot-2021-02-06-at-6.25.52-PM.png)