Windows comes with a small list of trusted CAs installed but automatically imports CAs as necessary from the Microsoft Windows Update service (Windows 7 Home Premium SP1 64bit for a while, I figure I’d imported all of the CAs I really need I figured I could mitigate the risk of forged certificates (e.g. Iraq/Gmail, Diginotar) by ensuring I don’t import any additional CAs. Sure the CAs I already trust could be compromised, but this significantly reduces the attack surface.
For Windows 7 Processional and Ultimate, Microsoft provides instructions for disabling Automatic Root Certificates Update using the Group Policy Editor; however, the Group Policy Editor cannot be installed on Windows 7 Starter and Home editions. If you have Windows 7 Starter or Home, or don’t want to deal with the Group Policy Editor, a simple registry update will turn Automatic Root Certificates Update off or on.
Note: You must be an Administrator to make any of these changes, and if you have a Group Policy set for Automatic Root Certificates Update, it will overwrite your registry changes.
I’ve created three .reg files you can download, and open to automatically update the correct registry keys:
- Disable.reg (view) – this disables Automatic Root Certificates Update.
- Enable.reg (view) – this disables Automatic Root Certificates Update.
- Remove.reg (view) – this removes the registry entry effectively enabling Automatic Root Certificates Update.
Note: You will most likely receive security warnings downloading and opening these files. If you want to be safe, open the files in a text editor and double check the contents.
If you would rather directly edit your registry, do the following:
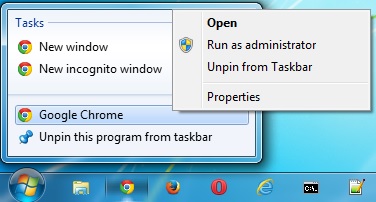
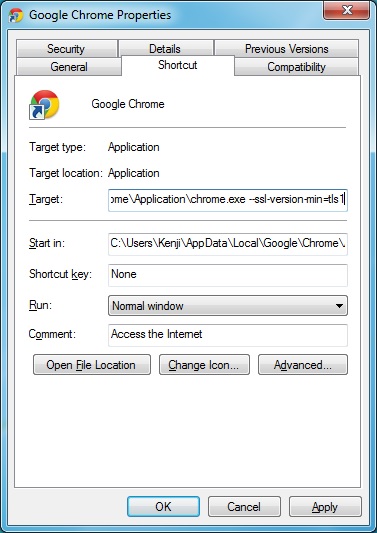
- Start regedit by clicking the Start menu, entering “regedit” in the search field, and pressing <enter>.
- Expand
HKEY_LOCAL_MACHINE/Software/Policies/Microsoft/SystemCertificates/AuthRoot
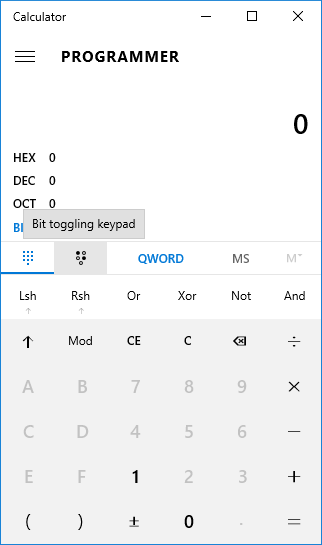
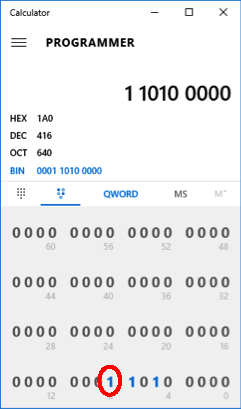
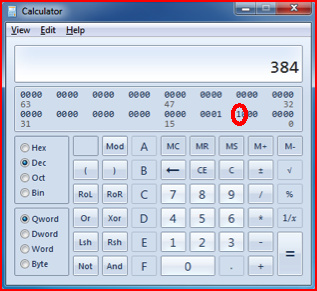
- Right-click on AuthRoot and select New -> DWORD (32-bit) Value
- Enter name: DisableRootAutoUpdate
- Double-click on DisableRootAutoUpdate
- Set the Value data to 1, click OK, and close regedit.
Deleting DisableRootAutoUpdate or setting it to 0, re-enables downloading new CAs from Microsoft.